From Space Glitches to Cyber Chaos: Hacks, Doxxing & Zero-Days.
13 April 2026BREACHAWARE HQ
A total of 15 breach events were found and analysed resulting in 5,702,310 exposed accounts containing a total of 25 different data types of personal datum. The breaches found publicly and freely available included Philippine Costumers, Citizens, Companies Database, Pivothealth, Kallningrad, ipapi.is and MyLovely.AI. Sign in to view the full
library of breach events which includes, where available, reference articles relating to
each breach.
Categories of Personal Data Discovered
Sociodemographic, Contact, Geolocation, Digital Behaviour, Technology, Career, Commerce, Unstructured, Communication Logs, National Identifiers.
Data Breach Impact
From broad consumer databases to niche services and AI platforms, the spread shows how varied (and persistent) the exposure landscape really is. For third-party organisations, it’s another nudge that risk doesn’t always come from headline-grabbing mega breaches, sometimes it’s the steady drip that does the damage. And for individuals, even smaller leaks can chip away at privacy, giving opportunists just enough to start connecting the dots. Less noise, same underlying threat.Cyber Update
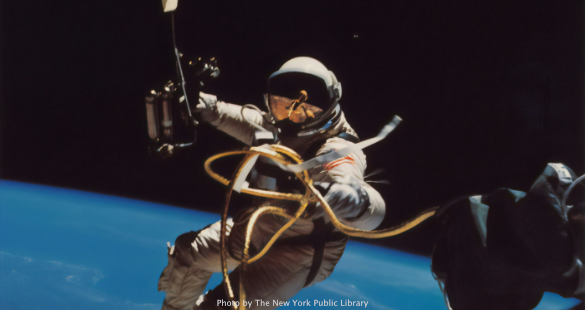
They can put a man on the moon… but apparently getting Microsoft Outlook to behave up there is still a work in progress.The Artemis II mission, launched last Wednesday, reportedly ran into a rather earthly issue: astronauts struggling to access their Microsoft accounts. Communication with NASA remained intact, but things took a turn when one astronaut summed it up perfectly:
“I have two Microsoft Outlooks and neither one is working.”
Microsoft 365 has been standard kit across NASA for years, but it turns out hurtling through space at 4,275 MPH isn’t exactly ideal for troubleshooting login issues. Somewhere, an IT support script is quietly suggesting: “Have you tried restarting the spacecraft?”
And the real question, what’s space travel without Microsoft Teams notifications?
Back on Earth, the BreachForums cinematic universe continues to deliver. We’ve already covered the chaos around N/A, the former admin who attempted an exit scam worth around $4,000, a modest sum considering the scale of the ecosystem. At first, it looked like your standard disgruntled insider situation.
It wasn’t.
ShinyHunters have now escalated things significantly, alleging that N/A is in fact a Bulgarian cybersecurity specialist and ethical hacker. Not your typical basement operator, more of a wildcard with something to lose.
And lose it they might.
ShinyHunters reportedly dropped a full dox, including:
• LinkedIn profile
• Full name
• Date of birth
• Additional personal identifiers
If accurate, this isn’t just forum drama anymore, it’s career-ending territory, with very real legal consequences looming. All over what amounts to a relatively small-scale exit scam in cybercrime terms.
A reminder, if one was needed: In this ecosystem, burning bridges tends to burn everything else with it.
And since we’re already talking about Microsoft, they’ve found themselves in another slightly uncomfortable spotlight. In recent days, developer accounts for WireGuard and VeraCrypt were reportedly suspended. For context:
• WireGuard is a widely adopted VPN protocol, now used by providers like ProtonVPN and Mullvad,
• VeraCrypt is a staple in encryption and privacy tooling.
In short: not fringe projects.
Microsoft’s explanation? The accounts failed to complete KYC (Know Your Customer) verification requirements within the deadline. Simple enough, except the WireGuard developer claims no such communication or deadline was ever received, even after checking all correspondence.
The immediate impact is more than just administrative inconvenience:
• Developers may be unable to push updates or patches,
• Any existing vulnerabilities could remain unaddressed,
• Critical infrastructure tools are effectively left in limbo.
For the privacy and security community, this lands awkwardly. Tools designed to protect users are now dependent on platform policies that can, intentionally or otherwise, cut off their maintainers at short notice.
Software Vulnerabilities
Fortinet FortiOS / SSL VPN; authentication bypass (active exploitation, KEV).Fortinet is once again refusing to stay out of the headlines. A fresh authentication bypass affecting SSL VPN components has been actively exploited, giving attackers a clean path straight into corporate networks. Perimeter security? More like perimeter suggestion. Patch immediately, disable exposed VPN interfaces where possible, and review login activity for anything suspiciously “successful.”
Microsoft SharePoint; privilege escalation / RCE chain.
SharePoint decided to remind everyone it’s still a high-value target. A vulnerability chain allowing privilege escalation and potential remote code execution has been flagged, particularly concerning for internet-facing deployments. Apply updates urgently and audit for unusual file uploads or admin activity.
Cisco Adaptive Security Appliance (ASA); remote access flaw (KEV).
Cisco ASA devices are back in the KEV catalogue thanks to active exploitation. Attackers are targeting remote access features to gain footholds in enterprise networks, because if you can get in through the firewall, why bother with anything else? Patch, restrict remote access, and review configs for unauthorised changes.
Apache OFBiz; authentication bypass / RCE (continued exploitation).
OFBiz continues its unexpected rise to fame as attackers keep exploiting known flaws. This week saw renewed activity targeting unpatched instances, reinforcing the idea that “we’ll patch later” is essentially an open invitation. Update immediately and check for web shells or unusual service behaviour.
Ivanti Connect Secure; post-exploitation persistence techniques evolving.
Not a brand-new bug, but a notable escalation. Attackers are refining persistence mechanisms in compromised Ivanti environments, making detection and remediation trickier. Fixing the vulnerability is step one, evicting the intruder is the real challenge. Conduct full forensic reviews, not just patching. Assume persistence unless proven otherwise.
Data & Privacy Headlines
AI regulation edges closer to enforcement reality.Across the EU and UK, discussions are shifting from “how should we regulate AI?” to “who’s getting fined first?” Organisations deploying AI systems with questionable data practices should start preparing for more than just polite guidance.
Cross-border data transfers back under the microscope.
Regulators are revisiting how data flows between regions, particularly between the EU, UK, and US. Expect more scrutiny, more paperwork, and fewer assumptions that existing frameworks will quietly hold.
The biometrics debate refuses to die (and is getting louder).
Age verification, identity checks, and facial recognition systems continue to spark debate. Regulators and privacy advocates are increasingly aligned on one thing: collecting highly sensitive data at scale is risky business, no matter how noble the intention.
Ransomware groups leaning harder into data extortion.
The shift from “encrypt and demand payment” to “steal, leak, and embarrass” continues to accelerate. Privacy is now the primary leverage, not just system availability. If your data gets taken, the real damage might come later, very publicly.
Supply chain risk now a board-level problem.
Another week, another reminder that third-party vendors are often the weakest link. Executives are finally paying attention, largely because regulators and customers are starting to ask uncomfortable questions about who exactly has access to their data.
Smarter Protection Starts with Awareness
Third-party exposure is now a first-order risk. You can’t patch what you can’t see.Free Data Breach Exposure Scan: Check any domain in seconds: https://breachaware.com/scan